This site uses cookies. By continuing to browse the site you are agreeing to our use of cookies Find out more here
Posts
Moving to a KVM Cloud : Conquer your fears and cut your...
Many organizations are looking for lower-cost and more easily manageable alternatives...
AI vs AI : Transforming Cybersecurity Through Proactive...
IT professional, you have the power to turn the tables. Now is the time to leverage...
The Modern Kill Chain: How Attacks Have Gone From Months...
Cloud breaches are now happening in minutes, not months. Threat actors are exploiting...
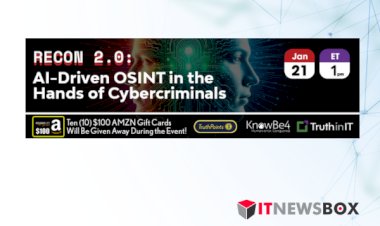
Recon 2.0: AI-Driven OSINT in the Hands of Cybercriminals
Cybercriminals are using simple artificial intelligence (AI) as well as generative...
Building a Culture Of Automation Intercom's Success Story...
This session delves into the technical and strategic aspects of integrating Tines...
AI For Smarter IT Workflows A Tines Platform Overview
It includes practical demonstrations and insights regarding the new AI capabilities...
Tines AI Transforms CrowdStrike Alert Management
With Tines, you can isolate and organize threat data
Automate Device Check CrowdStrike Integration in Jamf With...
This webinar highlights an automated solution to verify that CrowdStrike - or any...
NORTH KOREA'S SECRETE ARMY AND HOW TO COMBAT IT
These sophisticated operatives aim to earn high salaries while potentially stealing...
Assess Your AI Readiness How to Build your Foundation for...
This webinar equips you with the tools and strategies you need to accelerate your...